Your developers work for Cyber Gangs
Your developers work for cyber gangs Well, not deliberately. But if they’re building software with open-source components, there’s a chance that what they shipped last month included code placed there by criminals. And neither they nor you may know. If your organisation builds or customises software (and almost every organisation does, even if it’s just […]
Your website provider handles payments. Are you accepting the risk?

Your MSP handles the payments but are you accepting the risk? If your website provider told you not to worry about PCI DSS because “we handle the payments”… and you haven’t asked for proof …you might need to start worrying. It’s one of the most common things we hear from businesses: “Our managed service provider […]
Why ransomware victims pay, and what smart organisations do instead

Why ransomware victims pay, and what smart organisations do instead Ransomware extortion follows rational economics, not random chaos. When assets are valuable, defences are weak, and consequences for attackers are low, extortion thrives. This pattern holds whether the extortionist is the Sicilian Cosa Nostra or a ransomware group operating from a server in St Petersburg. […]
Why your staff click spelling-mistake laden emails (and how to actually stop them)

Why your staff click spelling mistake-laden emails (and how to actually stop them) You have done everything “right” by the book… “Cyber Awareness” training modules… posters in the lunchroom… even warning emails about the latest package-delivery scams. Yet, when the phishing simulation results come back (or worse, when a real incident report lands on your desk […]
Proxied Execution via Custom Trace Listeners
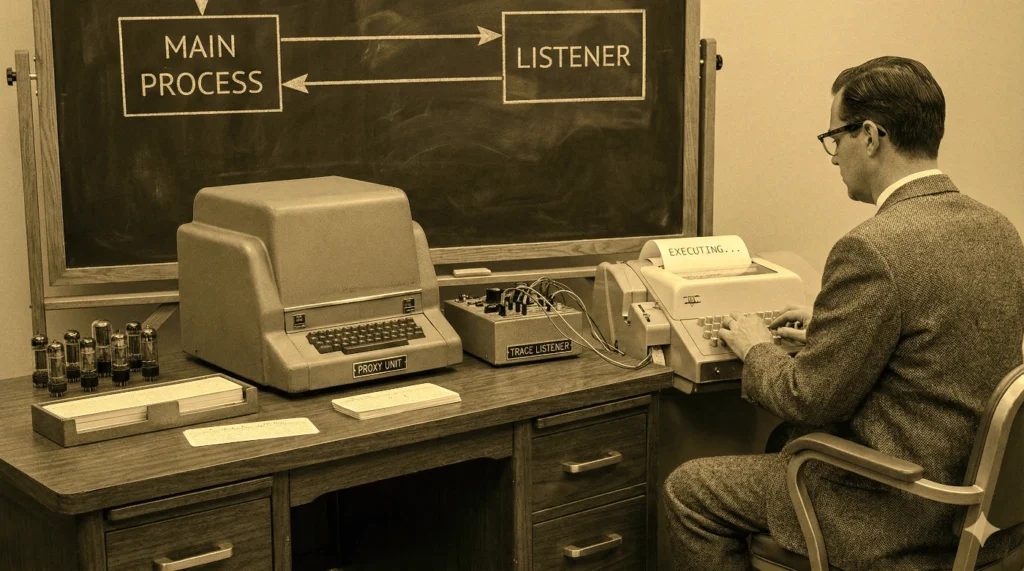
Proxied Execution via Custom Trace Listeners Our ongoing work into assumed-breach and adversary-emulation tactics provide the meat for this post, the first in a new two-part series. In summary: System.Diagnostics.Debug/Trace classes can be used to debug or instrument .NET executables/DLLs. Custom TraceListener .NET DLLs can be loaded via configuration. Some trusted signed (Production) executables on […]
Case study: data loss detection for national law firm

Case study: data exfiltration detection for national law firm Customer: National Australian law firm Service: Implementation of data exfiltration detections for Splunk Enterprise Security (ES) Outcome: Practical, always-on detections that surface suspicious data movement across cloud services, endpoints, and network activity Contact us > Background and context Data exfiltration is one of the hardest security […]
Managed SOC/SIEM use cases

Managed SOC/SIEM use cases This video walks us through four SIEM case studies that show how SIEM can strengthens security operations and prevent costly incidents. Take eight minutes out of your day to see and hear about some of our past SIEM security projects (both preventative and responsive) that show how SIEM and MDR solutions effectively […]
ASIC sues for systemic and prolonged cybersecurity failures
ASIC sues FIIG for systemic and prolonged security failures ASIC has commenced a law suit in the Federal Court of Australia. ASIC alleges that from March 2019 to 8 June 2023, FIIG Securities Limited failed to take the appropriate steps, as is required by an Australian Financial Services (AFS) licensee, to ensure it had adequate […]
SIEM solutions for incident management

SIEM solutions for incident management – Use cases This article examines practical use cases: How we’ve used SIEM solutions for incident management. It demonstrate how SIEM strengthens security operations and prevents costly incidents. Security Information and Event Management (SIEM) solutions are often seen as complex and expensive. However, their true value lies in mitigating financial, […]
The human factor: How to undermine your PCI DSS compliance

How to undermine your pCI DSS compliance efforts When it comes to PCI DSS compliance, most organisations focus on technical controls such as firewalls, encryption, and monitoring tools, to secure cardholder data. However, even the most advanced technical safeguards can be rendered useless if employees mishandle cardholder data due to a lack of training. Newer […]
