Dangling DNS (3) – The final pluck!

Dangling DNS (part 3) – The final pluck! In the final (?) part of our investigation into dangling DNS records and the risk that they present to organisations, we’ll review ‘elastic’ IP addresses as supported by the various cloud providers including AWS, Azure and Google Cloud. For the most part (because we’re most familiar with […]
Dangling DNS (2) – Still dangling!

Dangling DNS (part 2) – Still dangling! In our previous Dangling DNS records post, we examined the risks of leaving ‘dangling’ CNAME records pointing to DNS zones which are not under the domain-owner’s sole control. The consequences include increased risk of successful phishing attacks as well as reputational damage. The examples given in that post focused […]
Dangling DNS (1) – Abandon, despair!
Dangling DNS (part 1) – Abandon and dispair! Recently, there has been some interesting news describing how attackers have been able to take over various subdomains by taking advantage of dangling DNS records. To recap, this is a security mis-configuration issue: A victim organisation sets up (perhaps in a testing scenario) a service on a […]
Sophisticated, state-based actors?

Sophisticated, state-based cyber actors? As you will be aware of by now, the Prime Minister warned Australians of “sophisticated, state-based cyber actors” targeting Australian organisations and all tiers of government. But is the sky really falling and if it is, will we all be equally devastated when it crashes down? And what are the risks […]
Security for Australian law firms

2023 State of Cyber Maturity for Australian Law Firms The 2023 State of Cyber Maturity for Australian Law Firms survey invited legal professionals to share their approaches, motivations, decision making, and management towards cyber security. DotSec commissioned independent market research firm Momentum Intelligence to conduct the survey in collaboration with Lawyers Weekly. The survey was conducted on behalf […]
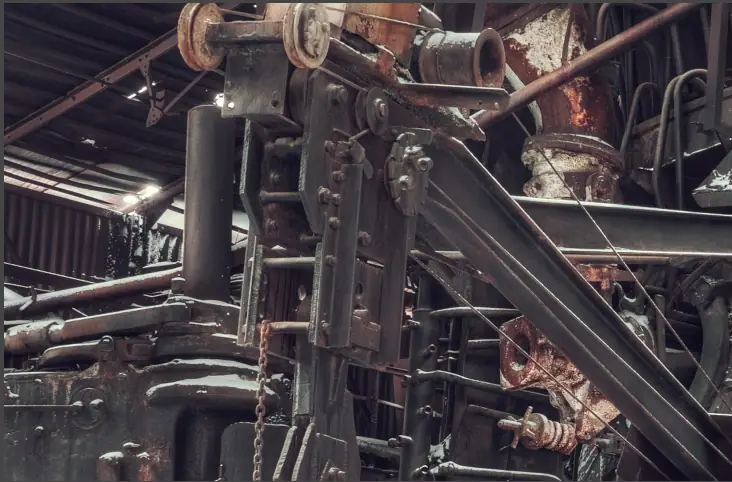
Magento as the coal-miner’s canary

Using Magento as the coal-miner’s canary Overview Regular review of web-application logs is not only a requirement for various compliance regimes (such as the PCI-DSS or various IRAP-based programs), it can actually give you good insight into vulnerabilities which arise outside of the web-application itself. In this post we describe how clever analysis of blocked-request […]
It’s still borked?
Neiman Marcus breach. Again. A long time ago*…… Waaay back, in 2013, high-end retailer Neiman Marcus was breached, resulting in a loss of data related to about 370,000 customers. Well needless to say, those 370,000-ish customers weren’t happy and they launched a class action claiming that Neiman Marcus was accountable for the breach which resulted […]
What? It’s borked?
When on earth did that happen? Can you imagine that a reputable organisation would deploy a business-critical security service without first designing and testing it, and then reviewing it to ensure that it operated as expected? Or, would you expect an organisation to allow a security service that was not well-designed, tested and regularly reviewed […]
