Bypassing Windows application whitelisting

Bypassing Windows application whitelisting This post describes how we discovered and reported to Microsoft an insecure deserialisation vulnerability in one of the binaries in the Windows Assessment and Deployment Kit (ADK), and how that can be used to bypass Application Control (native Windows application whitelisting). Application Control (formerly known as WDAC) is a native application […]
Why your staff click spelling-mistake laden emails (and how to actually stop them)

Why your staff click spelling mistake-laden emails (and how to actually stop them) You have done everything “right” by the book… “Cyber Awareness” training modules… posters in the lunchroom… even warning emails about the latest package-delivery scams. Yet, when the phishing simulation results come back (or worse, when a real incident report lands on your desk […]
Proxied Execution via Custom Trace Listeners
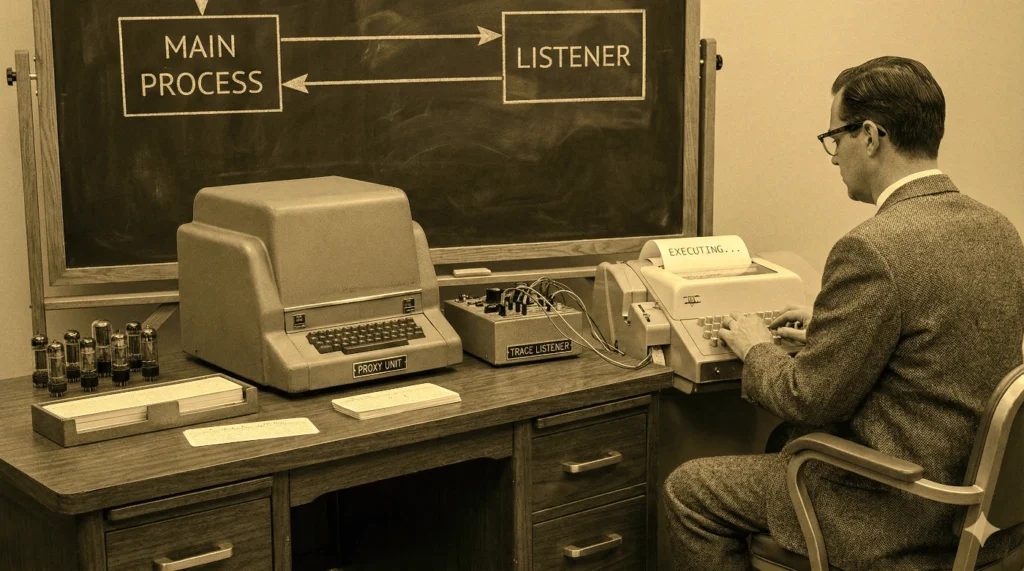
Proxied Execution via Custom Trace Listeners Our ongoing work into assumed-breach and adversary-emulation tactics provide the meat for this post, the first in a new two-part series. In summary: System.Diagnostics.Debug/Trace classes can be used to debug or instrument .NET executables/DLLs. Custom TraceListener .NET DLLs can be loaded via configuration. Some trusted signed (Production) executables on […]
DLL sideloading – Part 1

DLL Side loading – Part 1 This blog post is a result of our investigation into the process that attackers use when sideloading malicious DLLs into .NET executables. We’ll describe how and under what circumstances an attacker can get a malicious .NET DLL to be loaded by a trusted (signed) .NET executable, and we’ll also […]
Abusing Internet shortcuts for access and persistence

Abusing Internet shortcuts for access and persistence We’ve posted an update to this blog post, which we first wrote in 2025. In June 2025, Microsoft assigned CVE-2025-33053 (CVSS 8.8) to the .url file WorkingDirectory technique described in this post. The vulnerability was discovered being actively exploited by the Stealth Falcon (FruityArmor) APT group against government […]
SharpC2 in the real world

Sharpc2 in the real world As part of dotSec’s testing and assessment line of work, we undertake Red Teaming and EDR-evasion tests. In order to test EDR properly, we need to understand how to bypass it. This article documents practical methods for getting a SharpC2 .NET drone executable past Microsoft Defender by carefully applying obfuscation […]
DotSec’s AOC saves you money!
DotSec’s AOC saves you money! Payment card information remains one of the most targeted forms of data. For Australian organisations that store, process or transmit cardholder data, PCI DSS compliance is essential — not simply as an annual requirement, but as a way to reduce risk and improve the security of systems that support payment […]
Happy memories of an old hack
The good old (Internet banking Hack) days! So a long time ago (25 years ago actually!) in a research centre not so far away, I helped to write a paper that described an old Internet banking hack, outlined how the authentication systems that were used by browser-based internet banking applications could be bypassed and presented […]
Penetration testing over two years

Case study: Penetration testing over two years It was the great Gordon Ramsay that said, “I don’t like looking back. I’m always constantly looking forward. I’m not the one to sort of sit and cry over spilt milk. I’m too busy looking for the next cow.” But still, it can’t hurt to keep track of […]
It’s in the trees! It’s coming!

It’s in the trees! It’s coming! * Since March, we’ve been very busy providing incident-response and recovery services for organisations that have fallen victim to cyber crime. During that time, we have observed: Similarities in the security services, infrastructure and practices that were in place before the target organisations were compromised. Similarities in tactics and […]
