Overview
The Information-security Registered Assessors Program (IRAP) provides a framework that allows qualified and certified assessors to provide assessment services, particularly with reference to the Australian federal government’s Information Security Manual (ISM) and Protective Security Policy Framework (PSPF). The IRAP program is an initiative of the Australian Signals Directorate (ASD).
An increasingly wide range of businesses are being required to become compliant with controls (either all, or more usually, a subset) from the Australian federal government’s ISM and PSPF. From a private sector perspective, the ISM and PSPF are mostly relevant to businesses that provide services to the Australian government. The controls with which those businesses must comply are grouped together into what is known as a Statement of Applicability, or SOA. Sometimes a government department will define one or more SOAs and then require compliance with the SOA(s). On other occasions, the business will need to (in cooperation with an IRAP assessor, as described below) define their own SOA(s) before ensuring compliance with the SOA-defined controls.
IRAP assessments
In the earlier days of the IRAP program, IRAP assessment services were originally provided only to Australian government departments. Now however, IRAP assessment services are also provided to businesses that act as government service-providers such as hosting-service providers, education and employment service providers, and on-line (so-called “Cloud”) service providers.
The ASD’s IRAP assessment page describes the IRAP assessments as being a two-stage process:
An IRAP Assessor will assess the implementation, appropriateness and effectiveness of your system's security controls. This is achieved through two audit stages, as dictated in the ISM: - A Stage 1 Audit identifies security deficiencies which the system owner rectifies or mitigates. - A Stage 2 Audit assesses the residual compliance.
The page goes on to note:
In the Stage 1 Audit an IRAP Assessor ...defines the statement of applicability in consultation with the system owner ...etc.
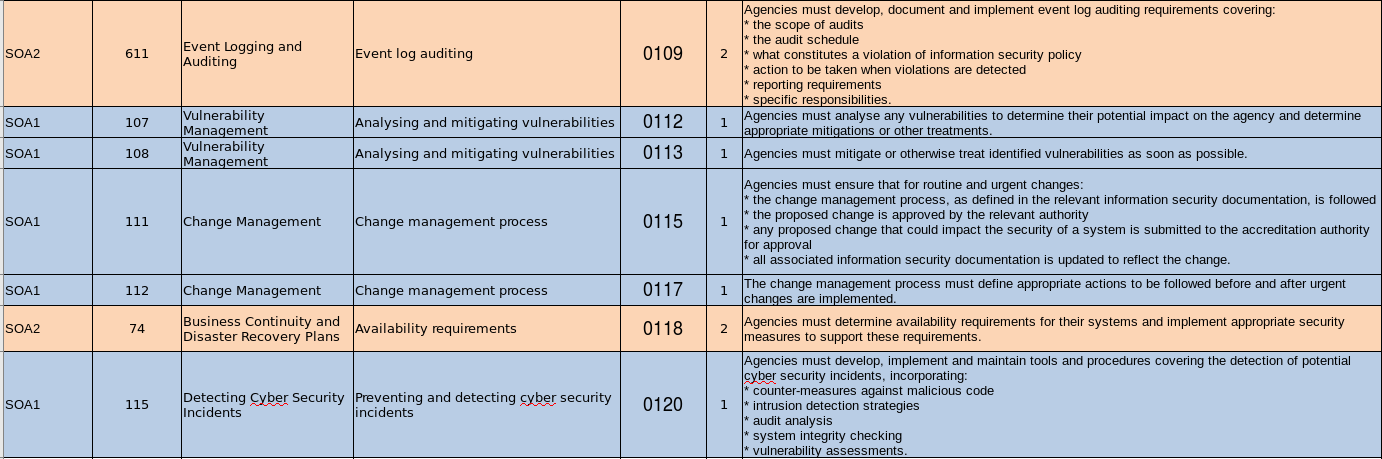
A variation to this approach occurs when a government department instead defines one or more SOAs, and the requires a service-provider business to comply with the controls that make up the SOA(s). At DotSec for example, we have seen this approach used for businesses in the Superannuation and Employment sectors. Here’s an example of a summary spreadsheet that shows a few of the controls with which one of the service providers needed to comply.
As you can see, the range of controls is quite broad, even in this small subset.
In fact, there are over 950 controls in the ISM, and these controls range across the following topics:
- Information security governance
- Physical security
- Personnel security
- Communications security
- Information technology security
The outcome of the assessment is a report to the certification authority that:
- Describes areas of compliance and non-compliance,
- Suggests remediation actions in the case that there are areas of non-compliance, and
- Makes a certification recommendation to the certification authority, which is generally associated with a government department.
We’ll provide a couple more IRAP-related posts in the future but for now, feel free to contact us if you are interested in understanding IRAP, the ISM and/or the PSPF further.