Why your staff click spelling-mistake laden emails (and how to actually stop them)

Why your staff click spelling mistake-laden emails (and how to actually stop them) You have done everything “right” by the book… “Cyber Awareness” training modules… posters in the lunchroom… even warning emails about the latest package-delivery scams. Yet, when the phishing simulation results come back (or worse, when a real incident report lands on your desk […]
Case study: data loss detection for national law firm

Case study: data exfiltration detection for national law firm Customer: National Australian law firm Service: Implementation of data exfiltration detections for Splunk Enterprise Security (ES) Outcome: Practical, always-on detections that surface suspicious data movement across cloud services, endpoints, and network activity Contact us > Background and context Data exfiltration is one of the hardest security […]
Case study: IRAP compliance

CASE STUDY: IRAP Compliance We’ve compiled a case study that summarises 18 months of very challenging, rewarding and ultimately successful work, guiding the development of an IRAP-compliant information security management practice. Our client was an international service-provider to governments in Australia and overseas. In order to be able to provide services to the Australian federal […]
Case study: Using SAQ A to ease PCI DSS compliance

USING SAQ A TO reduce your pci dss reporting load PCI DSS compliance reporting loads can be heavy going. Do you enjoy lots of PCI DSS reporting overhead? Do you like paying PCI QSAs a fortune? If so, this post is not for you! But if you want to save some time and money, read […]
2023 State of Cyber Maturity for Australian Law Firm
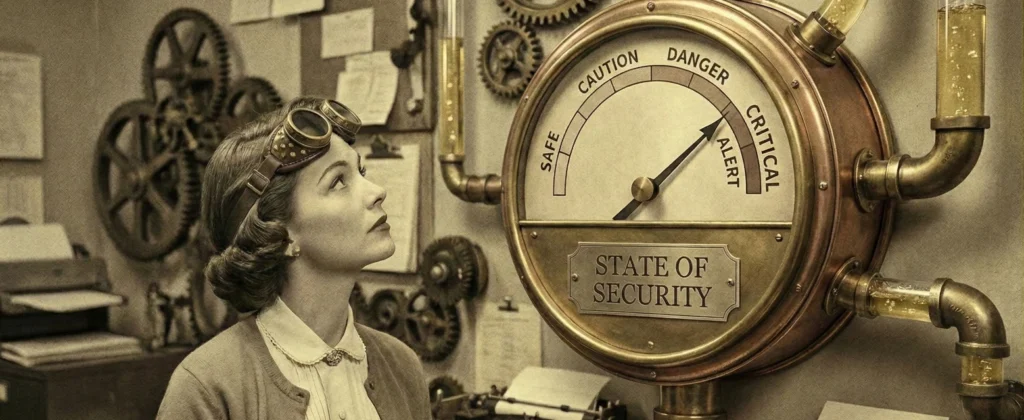
Case study: 2023 state of cyber for australian law firms Subject: Surveyed Australian law firms Summary: Findings which are grouped into three categories: Motivations (what makes the business push for better security) Maturity (how capable is the business when it comes to acting on their motivations) Management (how do those that run the business govern […]
Case study: Penetration testing for cross-business improvement

Case study: Penetration testing for cross-business improvement This case study describes how all our client’s businesses showed marked improvements in their cybersecurity posture after implementing a range of maturity-improvement recommendations. As we describe, dotSec’s assessors used the same guidelines and frameworks consistently across the various businesses over a two year period. As a result, our […]
Case study: ISO 27001 compliance

CASE STUDY: iso 27001 compliance We don’t just talk the ISO talk, we’ve walked the compliance walk and we’re ISO 27001-certified, so we know what it takes to implement and maintain a compliant ISMS. Our 27001 lead implementers and assessors have a wide range of certifications including PCI DSS QSA, ISO 27001, CISA, CISM and […]
